I have written extensively about the benefits of a holster. Since beginning work with the Sig P365XL I’ve discovered another one: a good, high-quality holster is an excellent administrative safety adjunct. Let me explain.
2021 Goal Progress: October
In January of 2021 I committed to some New Year’s resolutions: spend 15 minutes per day learning Spanish, workout 3 times per week, shoot my bow 3 times per week, read 73 books, and stay off tobacco. This is my progress so far in the year.
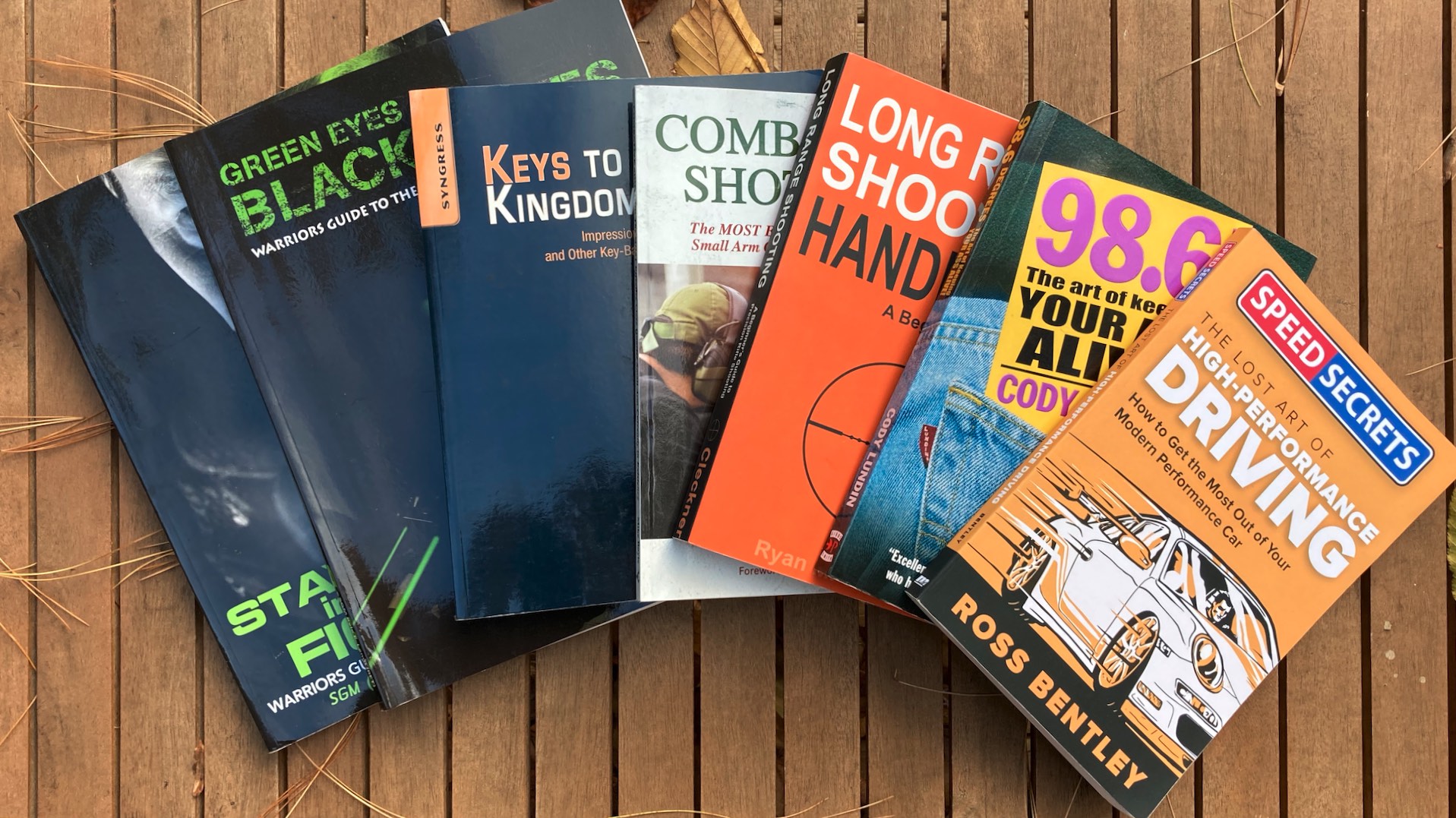
James Bond Night School Reading List
Since childhood I (and probably you) have fantasized about being a “competent man.” A competent man is good at everything – a Jason Bourne, MacGyver, Jack Reacher, or James Bond. He can seduce a woman, talk his way into anywhere, pick a lock, and operate any firearm at a high level. The competent man is in shape, can drive fast, speak foreign languages, and survive in the woods. Sadly, not all of us can be a secret agent. Most of us can find the time to read a book here and there. I give you the “James Bond Night School” reading list.
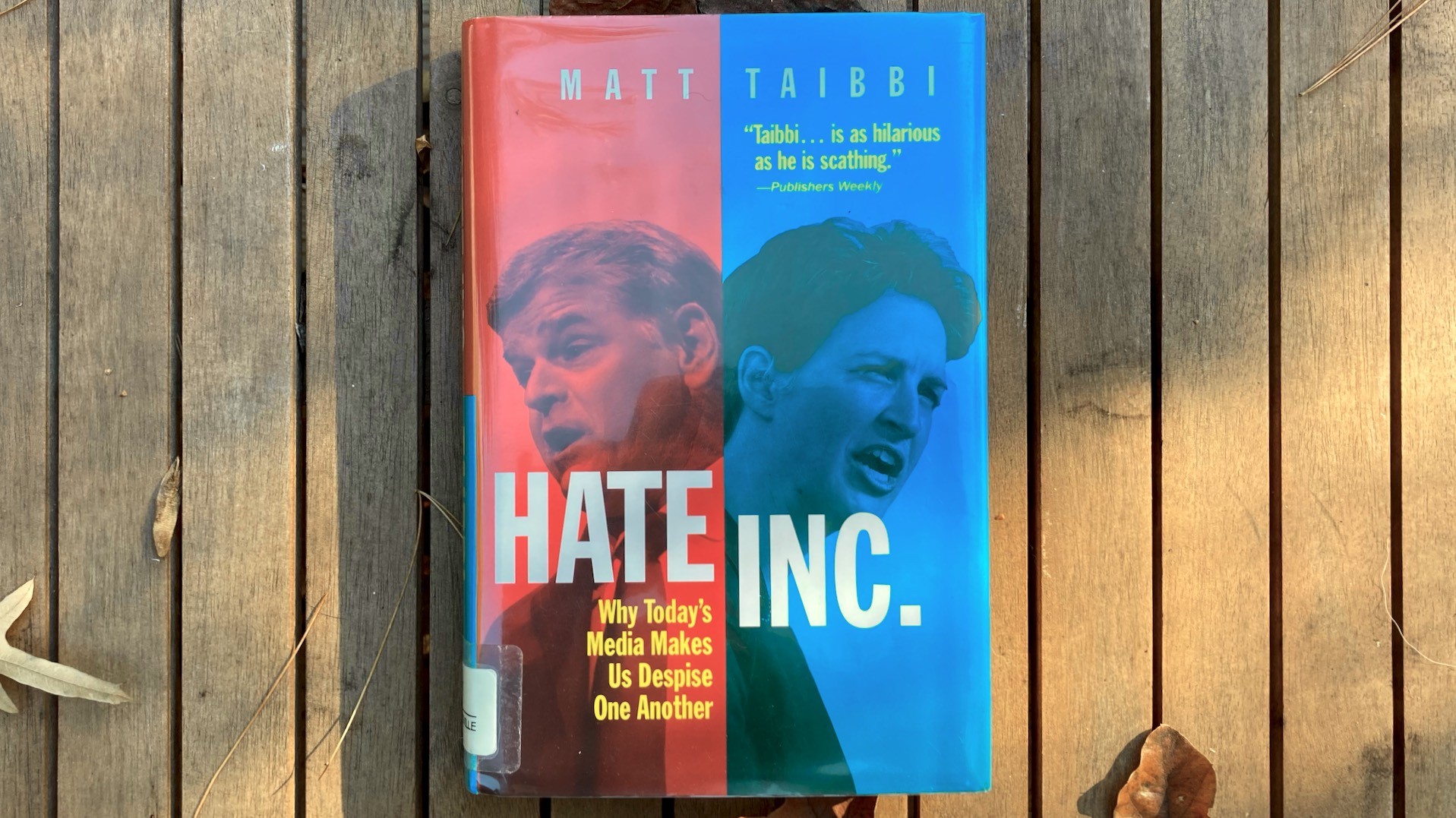
Hate Inc.: A Pretty Important Book
This week I finished Hate, Inc.: Why Today’s Media Makes us Despise One Another by Matt Taibbi. This is probably one of the most important books I’ve read in a long time. It explains how the media has divided us into two groups that are easy marks for advertisers. This is how media companies get rich reporting the “news.” It also explains the terrible cost of this wealth-building strategy.
Preparedness: A Realistic Bug Out Bag
The Bug Out Bag (bugout bag, B.O.B., or go bag) is the first place many people start with preparedness. Honestly, if it gets you started, GREAT – it’s a start! Unfortunately the bug out bag is often plagued with unrealistic expectations. Fantasies of “living off the land,” “heading for the hills,” and the “zombie apocalypse” too often color the concept of the bug out. Today I offer you a treatise on a much more useful, realistic bug out bag.
5 Steps to AMAG – (Actually) Make America Great
Many of you are dissatisfied with the results of last year’s Presidential election. As a political atheist and card-carrying “unaffiliated” I don’t have a dog in the fight. Most of you have sworn allegiance to a particular party and will support them now matter what they actually do, so allow me to offer you a bit of encouragement. Regardless of who holds the office of the President, the power to “make America great” resides where it always has: with The People. Here are some outstanding ways we can actually make America great.
2021 Goal Progress – September
In January of 2021 I committed to some New Year’s resolutions: spend 15 minutes per day learning Spanish, workout 3 times per week, shoot my bow 3 times per week, read 73 books, and stay off tobacco. This is my progress so far in the year.
Becoming a Paramedic
Today I write to you as a a fully-credentialed, practicing paramedic. This post is going to talk about how I got here, and the road to becoming a paramedic. I’ve written about this a little bit before, when I had just started school. There seems to be a lot of mystery about becoming a paramedic, so today I’d like to go into a bit more depth. Here’s my experience. Yours might be a bit different.
Survival Cooking: DIY Denatured Alcohol Stove
The soda can stove has always intrigued me. It’s about as cheap as a camping stove can possibly get: it takes about 30 minutes of your time and can be made from two soda cans. Fuel is also cheap; a gallon of denatured alcohol will cost you under $20 at Lowes. Today I’m going to talk about the infinitely accessible “soda can stove” or DIY denatured alcohol stove.
Build Rapport: Give a Toast and Tell a Joke
Several years ago I found myself needing to give a toast in front of a bunch of co-workers. I was able to give one, but it certainly wasn’t pretty. I vowed never to be in that scenario again. If ever again asked to make a toast, I would be ready. Likewise with a joke. Everyone should know how to give a toast and tell a joke. Let’s discuss.