An intrusion detection system (IDS) system should be an integral part of your home security plan. IDSs are detective security measures that also have a great deal of deterring value. Alarms are far more complicated than most people realize, however. To provide the maximum intended effectiveness, alarms must be carefully installed, tested, and used. These alarm system best practices will help you assess your own system or provide some guidance if having a new one installed.
This article has been updated and reposted. It was originally posted on October 25, 2015. Not too much has changed in the world of intrusion detection systems since this was written and the advice here is still really solid. I have added a bit more on DIY wireless systems as they have increased drastically in popularity over the last five years.

Alarm System Sensors
Sensors are obviously an important part of an alarm system. Sensors detect a change in state (open/closed, motion/no motion, etc.). There are two basic categories of sensors: point and volumetric. Point sensors are those sensors that monitor a specific point like a single door or window. Best practices for point sensors are simple: each door and window should be equipped with a point sensor, even on the second floor. A point sensor on a door should not allow it to open more than its own width without violating the sensor. Windows should not be able to be opened more than four inches without violating their sensors.

Volumetric sensors monitor an area rather than a single point. The passive infrared (PIR) motion sensors used in most residential applications fall into this category. So do sonic glass-break sensors. Best practices for volumetric sensors are: cover all large spaces (including attached garages), areas with multiple entry points, and any access to stairs.

Motion sensors are the most common type of volumetric sensors, and there are some special considerations for them. Motion sensors should be equipped with masking detection that violates the sensor if something is placed in front of it to blocks its field of “view”. Motion sensors should also have anti-tamper switches that alarm when the cover of the sensor is removed, or the sensor itself is removed from the wall.
Finally, the LEDs on volumetric sensors should be turned OFF when the system is operating normally. These are intended to allow you to “walk test” your system to determine what areas are protected by each sensor. Though leaving these LEDs on may give you confidence that your system is on and working, they also allow anyone with access to “walk test” your sensors and locate any dead areas in the coverage.
Sensors: Wired or Wireless
Sensors may be hardwired into your system (actual wires running between the sensor and control unit) or they may be wireless. While I generally prefer hardwired sensors to wireless ones, wireless sensors are much easier and more inexpensive to install post-construction. Wireless sensors have the disadvantage of being battery powered, and their signals may be detected and interfered with if not encrypted. If I were building a new home I would hardwire all of my sensors, but practicality usually dictates a few wireless sensors when upgrading an existing system.

Wireless signals present some problems if they are not encrypted. Unencrypted signals are vulnerable to interference/jamming. An attacker can replicate the signal to the control unit, telling it that the sensor has not been violated. Determining what companies do and do not encrypt their signals is difficult. If you are considering a particular company, ASK! Demand a clear, unambiguous answer, and don’t accept evasive statements like, “proprietary protocol.” Also, look for language in the contract that specifies signals have “jamming detection” or “tamper resistance”.
Alarm System Keypad/Head Unit
Control of the alarm panel keypad is, unsurprisingly, very important. Your alarm panel should be in a location that does not allow visual access from outside the home/office/etc. This can allow an intruder to tell whether your alarm is armed or not (a bad situation if the alarm is unarmed). It also allows someone to see the make and model of alarm panel you have, potentially allowing them to research vulnerabilities such as default codes for the panel.

Finally, though unlikely an intruder could potentially observe you inputting your code. If your alarm panel has a covered keypad, the cover should always remain closed. Otherwise it may be possible to observe wear patterns or dirt on the keys that could indicate which numbers are in the code, significantly narrowing down the possibilities.
Alarm System Codes
Your alarm system should allow at least two types of code: a standard use code (the code you use every day to arm and disarm your system) and a duress code.
Duress codes are one of the most commonly overlooked alarm system best practices. A duress code is a code that you can use under duress, i.e. if an intruder forces you to disarm your system. The duress code should alert the alarm monitoring station that you are being forced to disarm the panel under duress. The monitoring agency should immediately dispatch law enforcement without even a phone call to you; everything should appear perfectly normal to the intruder.
Monitored alarm systems will also typically have a phone password that the operator will request when calling you after your system goes into alarm. Unlike most passwords, this should be a pronounceable word that you can easily remember but it should not be something that is personally relatable to or easily researchable about you.
Both of these codes and the phone password should be well known to all of your family members. Outside of your family they should be treated as secret and protected exactly like other PINs, passwords, and codes. They should also be changed immediately if you experience a change in situation, such as a roommate or romantic partner moving out, or the firing of your babysitter/dog-walker/housekeeper; otherwise they should be changed every year or so.
Key Fobs: Many alarm systems now come with key fobs that allow you to disarm the panel without entering a PIN. These do come with some small inherent security risk (risk of loss, signal interception, etc.) but this risk is minimal in most threat models.
Key fobs have the enormous benefit of being retrievable. If you have service providers coming into your home, you can give them a key fob and get it back when your relationship with them changes. If you give them a PIN, there is no way you can get the PIN back. Instead you have to change it, and ensure that everyone in your family is aware of the change and has memorized the new one.
Arming and Disarming
If you have an alarm system you should use it. You should use it even when you are home. It is truly surprising to me how many people pay for an alarm system and arm it only rarely. There are two basic modes that most alarm systems can be set to: stay and away.
Stay Mode: When the alarm is in Stay mode all of the point sensors will generally be active but interior motion sensors will be inactive. In this mode the system should be set to go into alarm instantly upon violation of a sensor; otherwise an attacker has 30-60 seconds to force you to disarm the system before it goes into alarm (in which case you should use your duress code).
Away mode activates both the point sensors and all volumetric sensors, including motion and glass-break sensors. The away mode should be armed each time you leave the home. If you have large pets you should test your system to ensure you pets will not violate the volumetric sensors.
Communication Pathways & Monitoring
Communication pathways are methods used by the panel to communicate with the monitoring station. There are several types of communication pathways including standard and digital telephone lines, cellular, and TCP/IP (Internet). The best practice is to have redundant communication pathways.

In most residential applications this would be a physical telephone line and a cellular connection. Each has its advantages, and if you can only have one I recommend a cellular communicator. To ensure your alarm is working and communicating properly you should test it monthly. Be sure to call the alarm company before initiating a test so they can verify receipt of the alarm signal without dispatching emergency personnel.
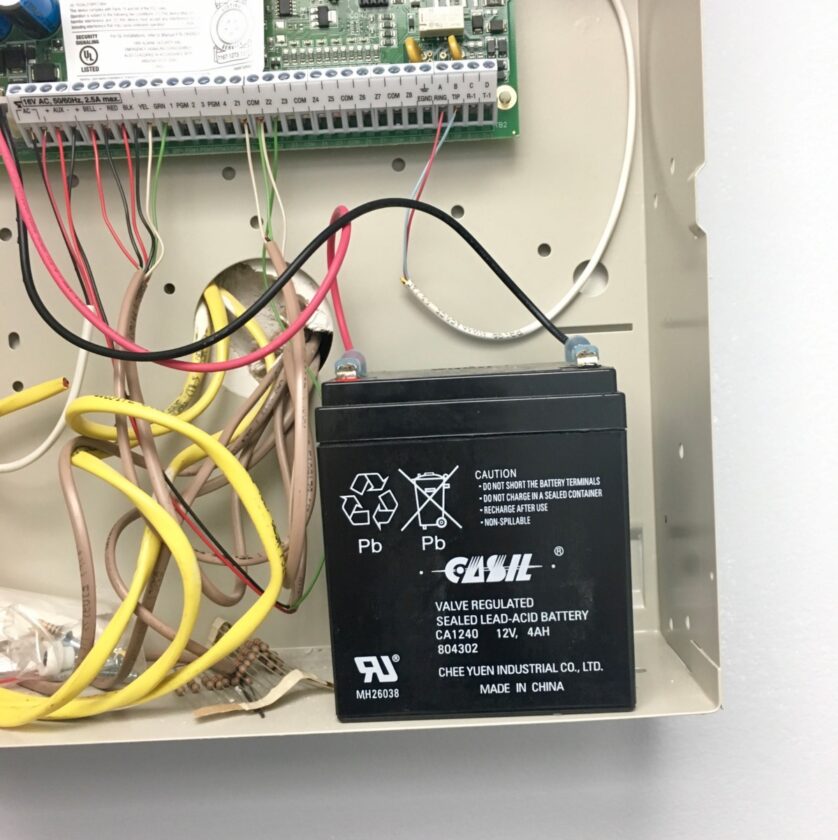
Alarm System Power
An alarm system requires power to operate and a power interruption not disable your system. A good alarm will be equipped a backup battery; the best practice for the battery is to ensure that it will power your alarm for a minimum of 24 hours. Seventy-two would be even better, ensuring you would be covered in the event of all but the longest outages.
Account Management
You must manage your alarm’s account (pay your bill) and most companies offer the standard options, mail and/or an online account. Management of you alarm’s account is very important. An attacker with access to your bill can learn important information about your system or potentially even cancel your monitoring service. If you receive your statements by mail I highly recommend sending them to your P.O. Box.
There are a number privacy and security benefits to using a P.O. Box instead of your physical address; in this instance it makes it much more difficult for the attacker to access your statement. If you choose to set up online account management you can opt out of paper statements (totally eliminating that vulnerability). However, you must ensure that you protect the account with a good, strong password and any other steps you can take to harden the account.
Alarm System/Company Recommendations
Unfortunately, I am unable to recommend any specific alarm companies or systems at this time. DIY systems like those from companies like SimpliSafe” are advertised heavily and have achieved some popularity. There is enough negative attention to give me pause with these systems.
Though I haven’t verified this, there are reports of these companies farming out monitoring to third parties. These third parties can potentially obtain a great deal of information about you. This is especially true when these systems are packaged with security cameras with audio capabilities. And as I mentioned earlier, many of these systems don’t encrypt signals.
In Summary
It is important to understand what an alarm can and cannot do for your security, even when you employ alarm system best practices. An alarm can be a deterrent to attackers in Level I and give pause to attackers in Levels II and II (assuming they don’t know the arm/disarm code). Just as importantly, and alarm is a detective control that will let you (and others) know if an entry is attempted against your home. It will also alert responders, limiting the time the attacker may spend there.
It is important to understand, however, that an alarm is a reactive control and does not make your home any more difficult to enter if the attacker isn’t concerned about alerting others. Even so, an alarm is one more very solid layer in a layered defense, provided you use these alarm system best practices.