I recently reviewed the Apricorn Aegis SecureKey flash drive and was extremely impressed with its security features. More recently I’ve had the opportunity to work with the Aegis Fortress L3 Secure solid-state drive. Today’s article will take a look at this device.
Disclosure: Apricorn reached out to me, unsolicited, after my review of the Aegis SecureKey flash drive. They provided this hard drive for review, free of charge. I have not received or been promised any compensation for Apricorn in exchange for this review. However, this article contains affiliate links.
Aegis Fortress L3 SSD
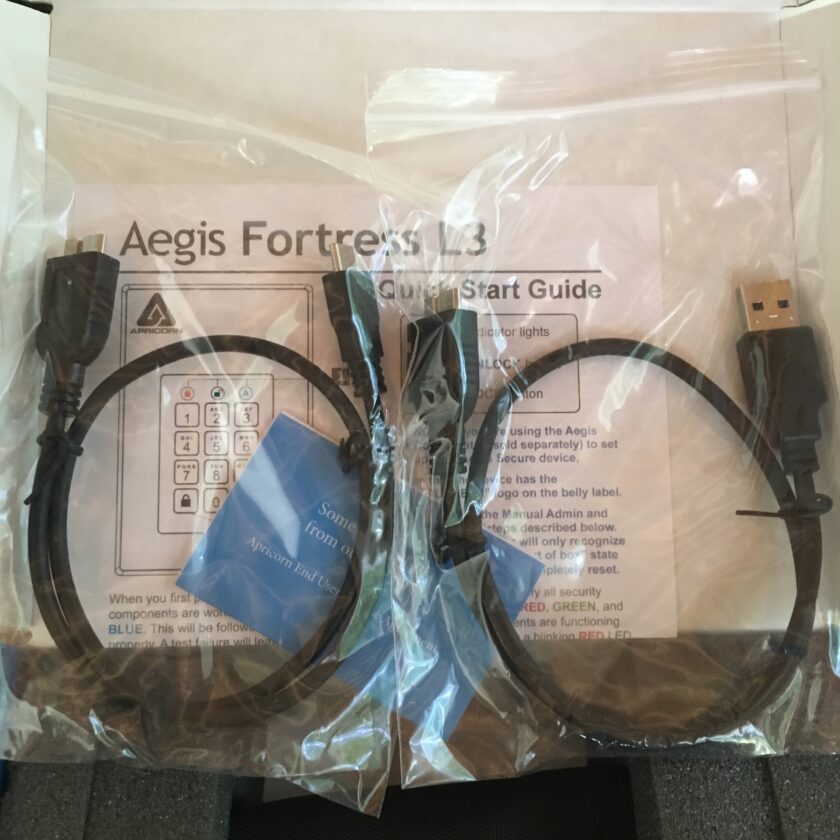
The Aegis Fortress L3 SSD ships with the same tamper-evident seal that the Aegis SecureKey did. The box is obviously larger to accommodate the larger drive, plus some cables. The Aegis Fortress L3 comes with both a standard USB 3.1 and a USB Type C cable. I had the opportunity to use both cables; the 3.1 on my older MacBook, and the Type C on my System76 Linux box.

Often overlooked in regards to data security is the longevity and damage-resistance of devices. It is abundantly clear this is not the case with the Aegis Fortress L3. It is housed in a sturdy 6061 aluminum-alloy case. The case is held together by one-way, breakaway, tamper-evident screws, and the screws are secured with a hardened epoxy. The Fortress L3 is currently pending IPxx review for dust- and water-resistance. Based on the performance of other Apricorn products (including the SecureKey 3z) I have no doubt it will perform well.
The Aegis Fortress L3 comes in a variety of sizes, ranging from 500 GB to 16 TB. Obviously, prices vary relative to storage size, beginning at an MSRP of $239 for the 500 GB drive, all the way up to $9,999 for the massive 16 TB model. Conveniently, the Aegis Fortress L3 can be purchased on Amazon.
It’s understandable to have a little sticker-shock at the cost of these devices. However, they really aren’t that expensive when compared with competing, non-secure products. In a direct comparison, an external, NON-secure 2 TB SSD from SanDisk cost $249 on Amazon. A 2 TB Samsung SSD comes it at $289. In fairness the Samsung advertises hardware encryption, but lacks FIPS validation, and requires running Samsung software for password input. At $339 the 2 TB Aegis Fortress L3 is a bit more expensive than both, and I think the added cost is completely justified.
Aegis Fortress L3 Security
The security is what makes this drive worth the extra money. The core of this security is the very conspicuous PIN pad on the face of the drive, and the drive’s hardware encryption system. The PIN pad accepts a PIN between 7 and 16 digits. Like the SecureKey, the device cannot be used without a PIN, and PINs cannot be repeating digits (i.e. 1-1-1-1-1-1-1) or sequential digits. The device comes with no PIN installed, and will not function until one is set.
The onboard PIN entry comes with a couple huge benefits. First, if the computer you are about to attach the Aegis Fortress to has a keylogger, you’re still safe. A keylogger on the computer won’t capture the Aegis’s PIN. The next benefit is that the information is encrypted on hardware before being written to the drive. This means that no software is required to run in order to make your data cryptographically accessible.
Personally, I recommend using the longest possible PIN (16 digits). I also recommend pseudorandomly generating your PIN with a program like KeePassXC. I would generate several, and choose one that contained every digit to avoid wearing certain numbers more quickly than others.
Not only does this make the data more secure by tying it cryptographically to the device, it also has some other benefits. This means you can format the drive completely. The Aegis can be formatted into NFTS, macOS Extended (Journaled), exFAT, etc. With more common drives, formatting would erase the necessary encryption software.
The Aegis Fortress must be setup with an administrator password. A separate, user password can also be established. I recommend making both passcodes, and logging in as the user when simply accessing the drive. the Administrator PIN has the ability to change a number of the Aegis Fortress’s configurations.
Additional Security Features
The administrator PIN is useful for IT professionals setting these devices up for enterprise users. The Admin PIN is also necessary for home users. Entering the Admin PIN allows many of the advanced features of the Aegis Fortress L3 to be configured. These features are the ones most likely to excite long-time readers of this blog.
Unattended Auto-Lock: The Aegis SecureKey can be configured to automatically lock if not accessed after a predetermined period of time. By default the drive will remain unlocked as long as it is attached to a computer, until the lock button is pressed or it is ejected. To get the benefit of the Unattended auto-lock feature, you have to enable it. The unattended auto-lock can be programmed to lock the device after 5, 10, or 20 minutes.
Configurable Brute Force Protection: The Aegis SecureKey has a default brute-force protection limiting login attempts to 20. This number can be reduced, but cannot be increased, and the protection cannot be removed. The number of PIN attempts can be reduced to as few as four. I recommend lowering this number to no more than 10, and this becomes more important the shorter your PIN is.
Self-Destruct PIN: The self-destruct PIN is a tertiary PIN (in addition to the Admin and User PINs) that destroys all data on the device when entered. This PIN can be used under duress to ensure no data is recovered from the device. Like the Admin and User PINs the self-destruct PIN must be between 7 and 16 characters long.
When the self-destruct PIN is entered, all decryption keys will be destroyed. This will render any data on the drive cryptographically inaccessible. The drive will appear empty, but will also appear to function normally. The self-destruct PIN can be used to unlock it at will and new data can be written to it. This is a pretty clever feature; the data on the device can be destroyed without making it immediately apparent to an adversary that you’ve destroyed it.
Read-Only Mode: The ability to place the drive in read-only is really, really cool. This allows you to unlock the drive and attach it to untrusted (i.e. public or work) computers to access data. This provides a good layer of insurance that malware cannot be written to the drive. The drive can be placed in read-only mode in both the Admin and User modes.
Full Reset, Change PINs, etc.: Should you find yourself locked out of the device or simply wanting to start from scratch, you can.
Documentation and Validation
The Aegis Fortress L3 ships with a quick start guide. This guide explains how to set up the basic functions of the drive: first-time use, locking and unlocking the drive, adding a User PIN, and formatting for macOS. Additional features are documented in full in the Aegis Fortress L3 manual [opens to .pdf].
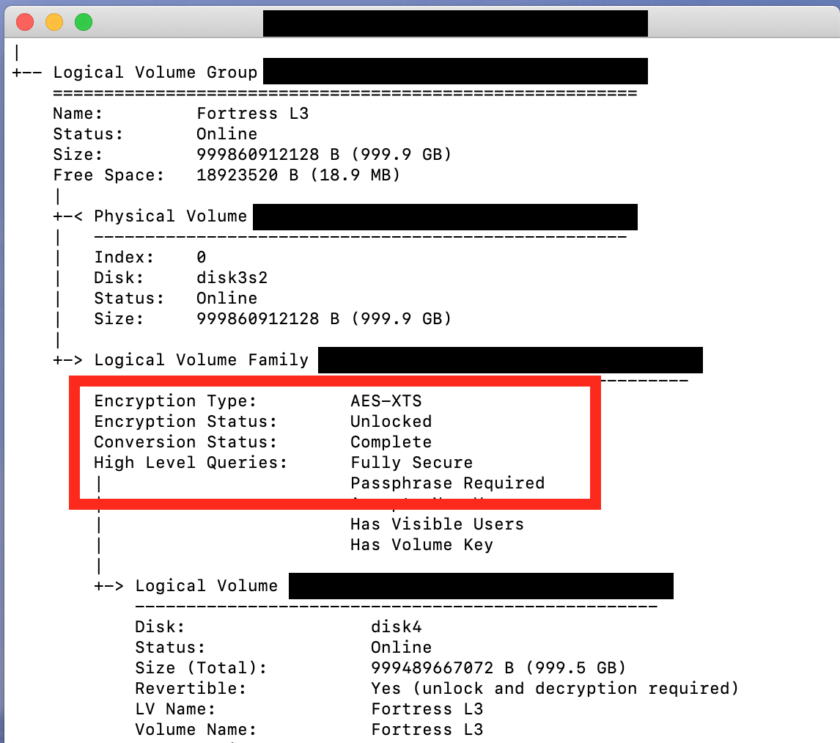
The Aegis Fortress L3 Secure SSD is currently undergoing FIPS validation. According to Apricorn, this device should meet FIPS 140-2 (Level 3) validation by Q3 of 2019. This is the highest level of security validation offered for portable devices, and is truly impressive.
My Use-Case and Impressions
Undoubtedly, this device is intended for enterprise and government customers. It is extremely expensive relative to “common” hard- and solid state drives. I am very happy that Apricorn is making these devices easily available to the public. This is perhaps the most robust solution to protecting data-at-rest I’ve seen.
Now I have two Apricorn products: a 128 GB Aegis SecureKey 3z that I paid for, and the 1 TB Aegis Fortress L3 that was provided to me by Apricorn. The SecureKey 3z stays in my travel electronics bag. This is the backup of my data that I take with me when I travel. This drive is updated daily when I am on the road, and weekly when I am at home. If this device were to be stolen I would have no concerns whatsoever that my data would be safe.

The Aegis Fortress L3 is my primary backup drive at home (for now; I need a larger one to accommodate all my data). It sits on my desk, and is almost always plugged into one of my two computers. When I leave home (either for travel or a night out) the drive goes in my safe. Thought I don’t want my stuff to be stolen, if it were I have zero doubts about the security of my data.
For a bit more security, I have added software full-disk encryption to both of these devices. That is one of the most important benefits of Apricorn’s 100% software-free encryption: you can format this drive in any manner you want, including fully encrypting it. I tried this with both VeraCrypt and macOS’s FileVault. Both mounted and performed perfectly.
ONE IMPORTANT NOTE: if you are keeping all backups behind Apricorn’s encryption, you need to have access to the PIN. Initially, when I only had the Aegis SecureKey, I was happy to leave the PIN in my password manager’s database, which was backed up in multiple locations. Now, in beginning to move all backup data to Apricorn devices, I’m much more aware of the need to memorize the PIN (or store it on another device). Memorizing it hasn’t proven to the that difficult; entering it on one or more of these devices daily is a great way to remember it.
In Summary
The Aegis Fortress L3, like the SecureKey flash drive, is an exceptionally well-made product. The security provided by the Aegis line’s hardware encryption (and perhaps a secondary layer of software encryption) is unparalleled. Going forward I will use nothing but Apricorn products for storage of my own data.